Political commentator and UK citizen Sami Hamdi was finally allowed by the US government to leave the US on November 12, two and a half weeks after he was arrested at San Francisco International Airport when he went to check in for a domestic US flight.
Mr. Hamdi had been a keynote speaker at the annual banquet of the Central Valley chapter of the Council on American Islamic Relations (CAIR) on October 25 in Sacramento, and was on his way to the next stop on his US speaking tour when he was taken into custody at SFO on October 26.
Mr. Hamdi had obtained a valid US visa prior to his arrival in the US. “Hamdi entered on a B-1/B-2 visa on October 19, 2025, and complied with inspection and admission”, according to the complaint filed on his behalf in Federal court during his detention.
No criminal charges were ever filed against Mr. Hamdi, and there has been no suggestion that he knew his visa had been revoked until he was taken into custody. The government has argued that issuance or revocation of any visa is entirely discretionary, and that once Mr. Hamdi’s was revoked, he was no longer legally entitled to remain in the US.
Even if that were factually and legally correct, it begs two important questions:
First, how did the immigration agents who arrested Mr. Hamdi at SFO know about his travel plans in order to intercept him?
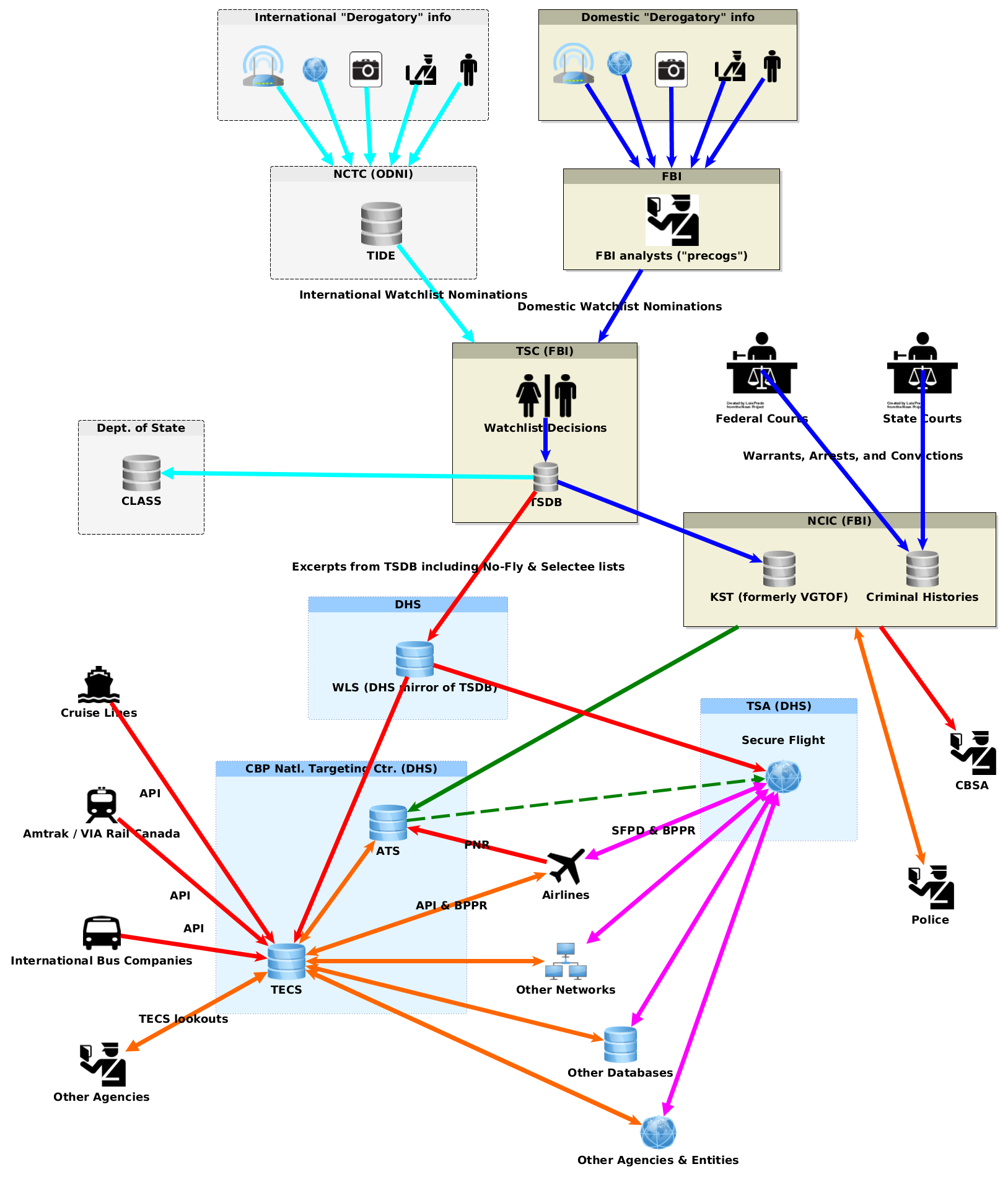
Federal agents can use a TECS alert to monitor reservations for international flights for a person of interest, even without any charges or any warrant for search or arrest. This appears to be how Dr. Mark Bray was targeted for questioning by Feds at Newark Airport on the second of his two attempts on successive days last month to flee the US with his family.
However, Mr. Hamdi went to SFO to check in for a domestic flight, not an international flight. The TSA has long wanted to check reservations for domestic flights against warrants listed in the FBI’s aggregated NCIC database. But so far as we can tell, that hasn’t yet been done. If it were, hundreds of air travelers would be arrested every day, given the number of records of arrest warrants — many of them obsolete or inaccurate — in NCIC.
And there’s been no hint that there were any criminal charges or any warrant – – even one based on a sealed indictment — against Mr. Hamdi. So a “warrant check” seems unlikely.
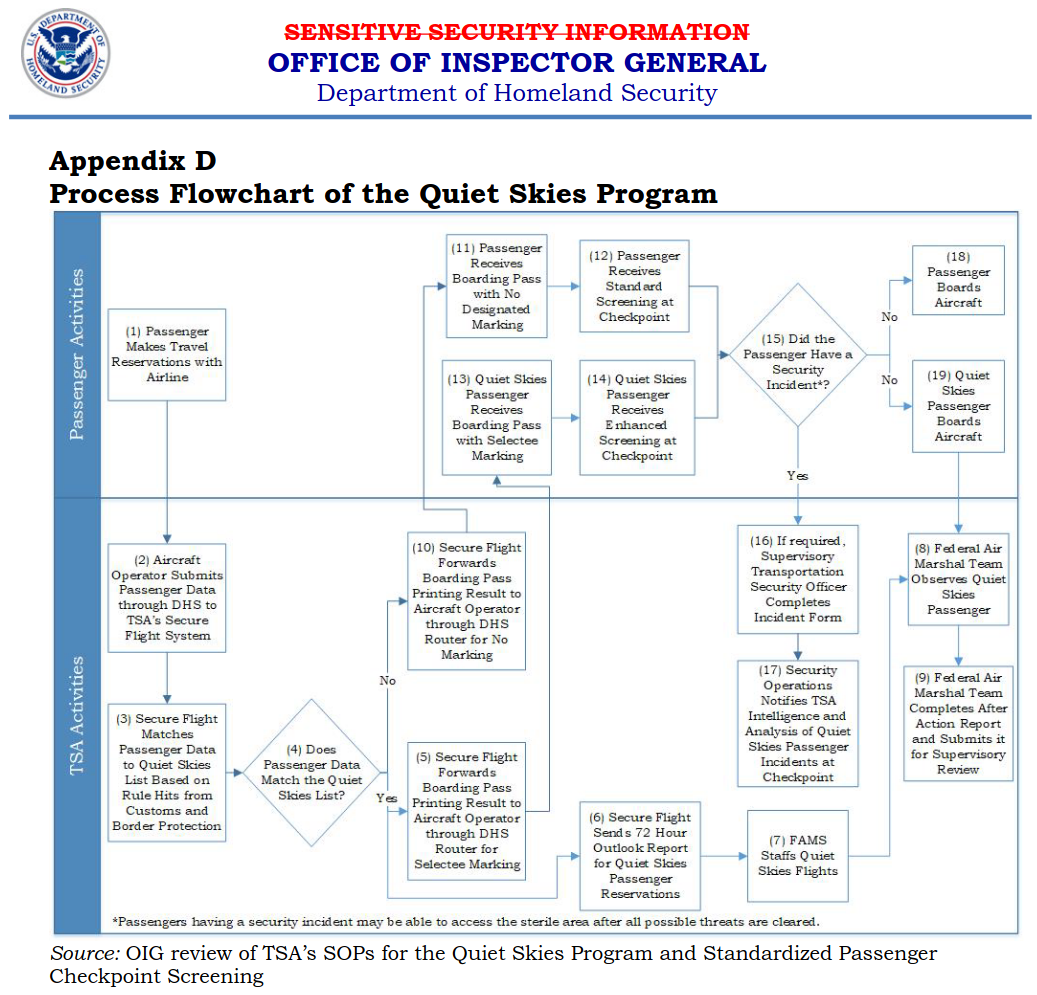
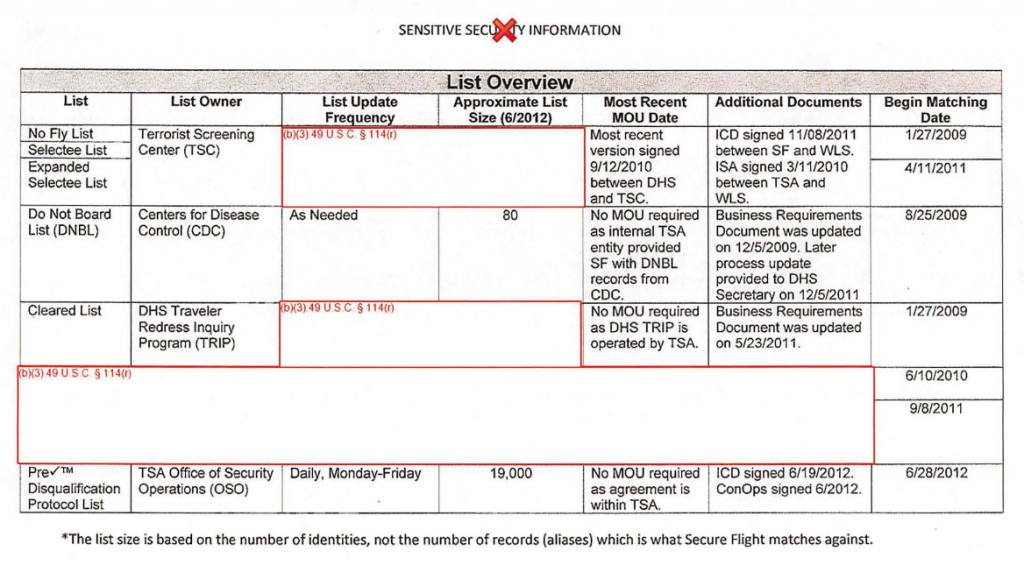
The lists that are checked whenever an airline sends Secure Flight Passenger Data for a domestic flight to the TSA, before the TSA returns a “Boarding Pass Printing Result” (BPPR) to the airline, are the “no-fly” and “selectee” lists which constitute a subset of the names in the Terrorist Screening Database.
We know that the no-fly and selectee lists have been used primarily to target Muslims. But as the name of the TSDB suggests, these are supposed to be used, and have been justified to courts as being used, solely for individuals who pose an identified threat to aviation security. There’s been no suggestion that Mr. Hamdi did anything to offend the US government or cause it to revoke his visa aside from saying things the US doesn’t want said, much less anything — no matter how offensive to anyone — that posed a threat to aviation security.
It thus seems likely — in the absence of any better explanation — that some Federal agency or official put Mr. Hamdi on the no-fly or selectee list as a way to use airports as a dragnet to catch him the next time he tried to fly, solely on the basis of pure speech that did not provide a basis for any criminal charges. If so, that was a gross abuse of the aviation “security” system and a significant foray into its use as a tool of political retaliation against disfavored speakers. If this could be done to Mr. Hamdi, it could be done to US citizens.
Second, why was Mr. Hamdi not allowed to leave the US sooner?
Normally, non-US citizens denied entry on arrival at US airports are detained only until they can be put on the first flight back to their port of embarkation for the US, or any earlier flight to that or any other destination for which they choose to buy a ticket.
There are five nonstop flights every day from San Francisco to London. Why, instead of being put on one of these flights the day he was detained, was Mr. Hamdi shipped in shackles to a private prison near Bakersfield and held there for more than two weeks?
Article 12 of the International Covenant on Civil and Political Rights, to which both the US and the UK are parties, provides that, “Everyone shall be free to leave any country, including his own.” And the UN Human Rights Committee has made clear that, “the scope of article 12, paragraph 2, is not restricted to persons lawfully within the territory of a State.”
So once Mr. Hamdi was deemed no longer entitled to remain in the US, and was not (and never had been) subject to any criminal charges, he had a right, as a matter of international human rights treaty law, to leave the US at any time and for any destination.
Mr. Hamdi’s eventual departure was described as “voluntary”. But it’s hard to see his leaving the country as uncoerced when they only alternative he was offered was to remain indefinitely imprisoned without charges or trial.
Detaining Mr. Hamdi without the opportunity to leave the country, and holding him for more than two weeks without letting him leave, was a clear violation of international law.